Command and Control (C2) frameworks are essential in the Red Teamers and Attackers playbooks. They help hackers of all types to take over networks or turn regular computers into bots, creating a network of remotely controlled computers that can send spam or launch DDoS attacks.
In the early days of the internet, a Command and Control attack would allow hackers to have full control of a physical server, now most of the targets are servers on the cloud.
We can easily imagine the catastrophic effects if an attacker gained access to public services servers, being able to shut down power supplies entirely, gaining control of computers that are responsible for handling robot-assisted surgeries at hospitals, and so on.
But how does a computer get infected?
There are numerous ways of infecting a computer and starting a C2 framework, and they are usually done through well-known ways.
- Malvertising
- Vulnerable web browser plugins
- Phishing
- Direct installation of malware (usually done through physical access)
- Exploiting a vulnerable system (usually due to unpatched OSs and servers)
After the infection is done, the attacker can launch a reverse shell in order to execute commands, start a ransomware attack, exfiltrate data, launch a DDoS attack or just sit there and wait for the appropriate moment to do their devilish things.
The Command and Control structure
As of now, everything might look overwhelming, but at the end of the day, a C2 server is pretty much a listener (C2 server) that can handle many reverse shells at once (C2 agents) plus the post-exploitation features that only the frameworks have.
A reverse shell or remote shell takes advantage of a vulnerability to instantiate a shell session and access the victim’s computer, in order to redirect inputs and outputs from the user’s computer to the attacker’s machine.
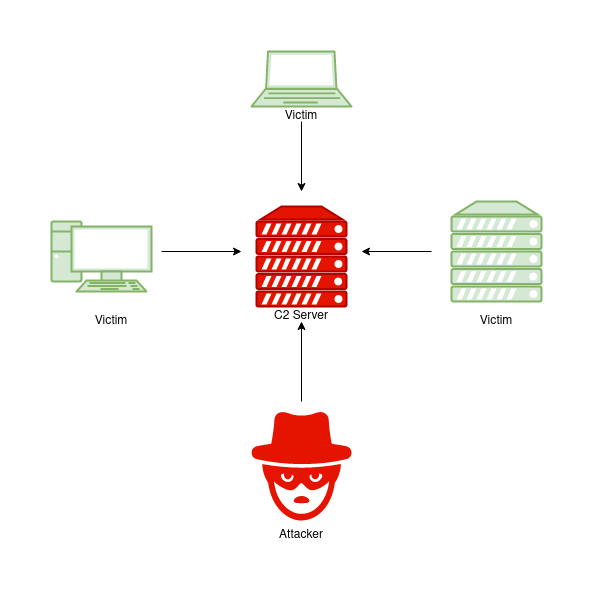
- C2 Server: Serves as a hub for the agents to call back to, agents will periodically call back to the server and wait for the operator’s commands.
- Agents/Payloads: The agent is generated by the framework and is responsible for calling back to the server. It has special functionalities that cannot be found on simple reverse shells.
- Listeners: As the name suggests, it’s an application that runs on the C2 servers and waits for a callback on a specific port or protocol.
- Beacons: This is the process of the Agent calling back to the server.
Most common C2 frameworks
There are free and paid frameworks, they have some differences, but probably the biggest one is that the premiums are less likely to be detected by antivirus software. That does not mean that the free ones are bad, but since they are open-source, signatures can easily be developed.
-
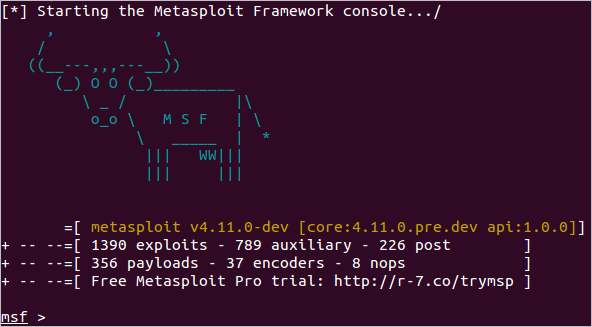
Metasploit: is one of the most popular frameworks, it’s developed and maintained by rapid7, it is publicly available, can be downloaded for free, and comes bundled in the most popular penetration testing distributions.
-
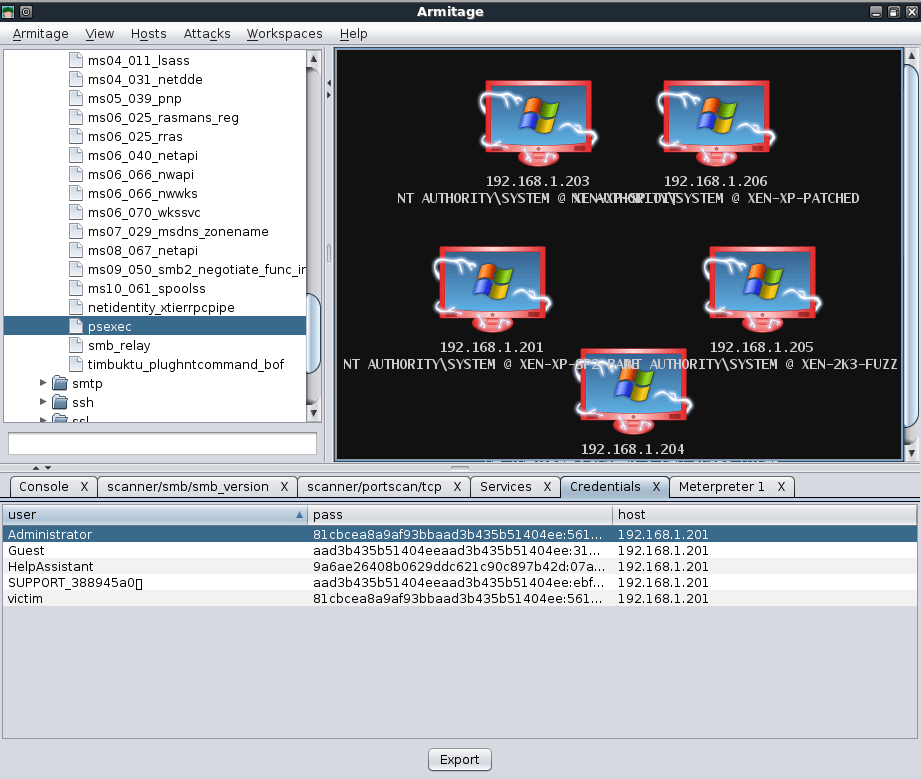
Armitage: This is an extension of the Metasploit framework, it has a fully-fledged GUI written in Java that looks similar to Cobalt Strike, this is because they are both created by Raphael Mudge.
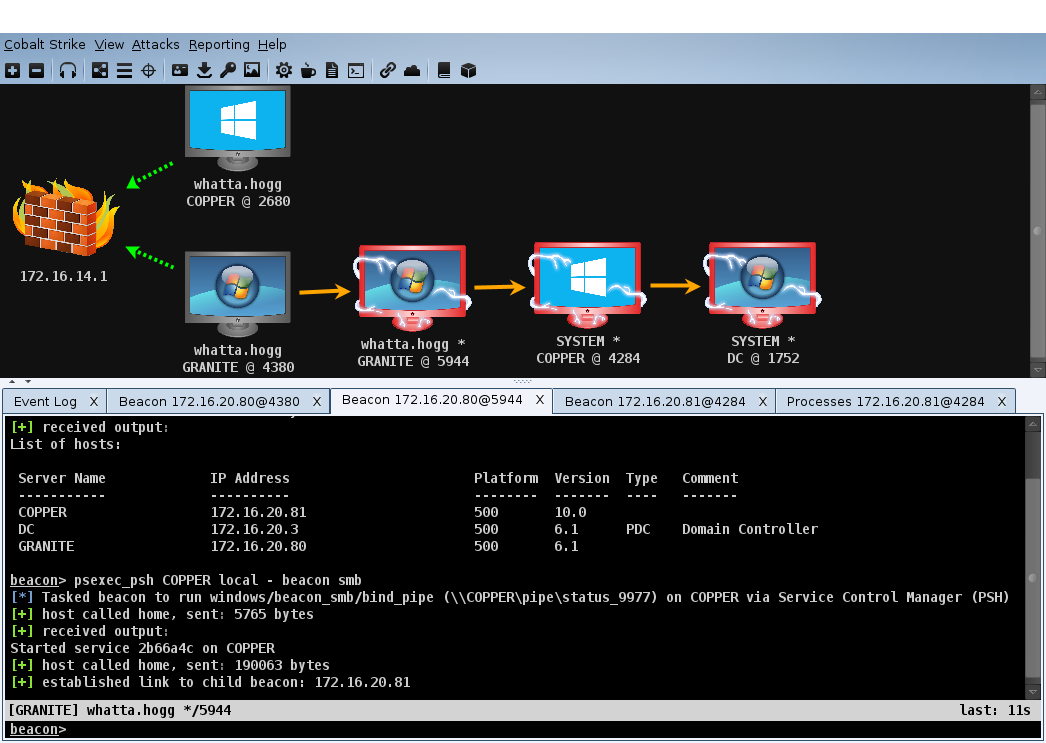
- Cobalt Strike: This is arguably the most popular C2 framework next to Metasploit, has its GUI written in Java to increase flexibility, and is maintained by HelpSystems.
-
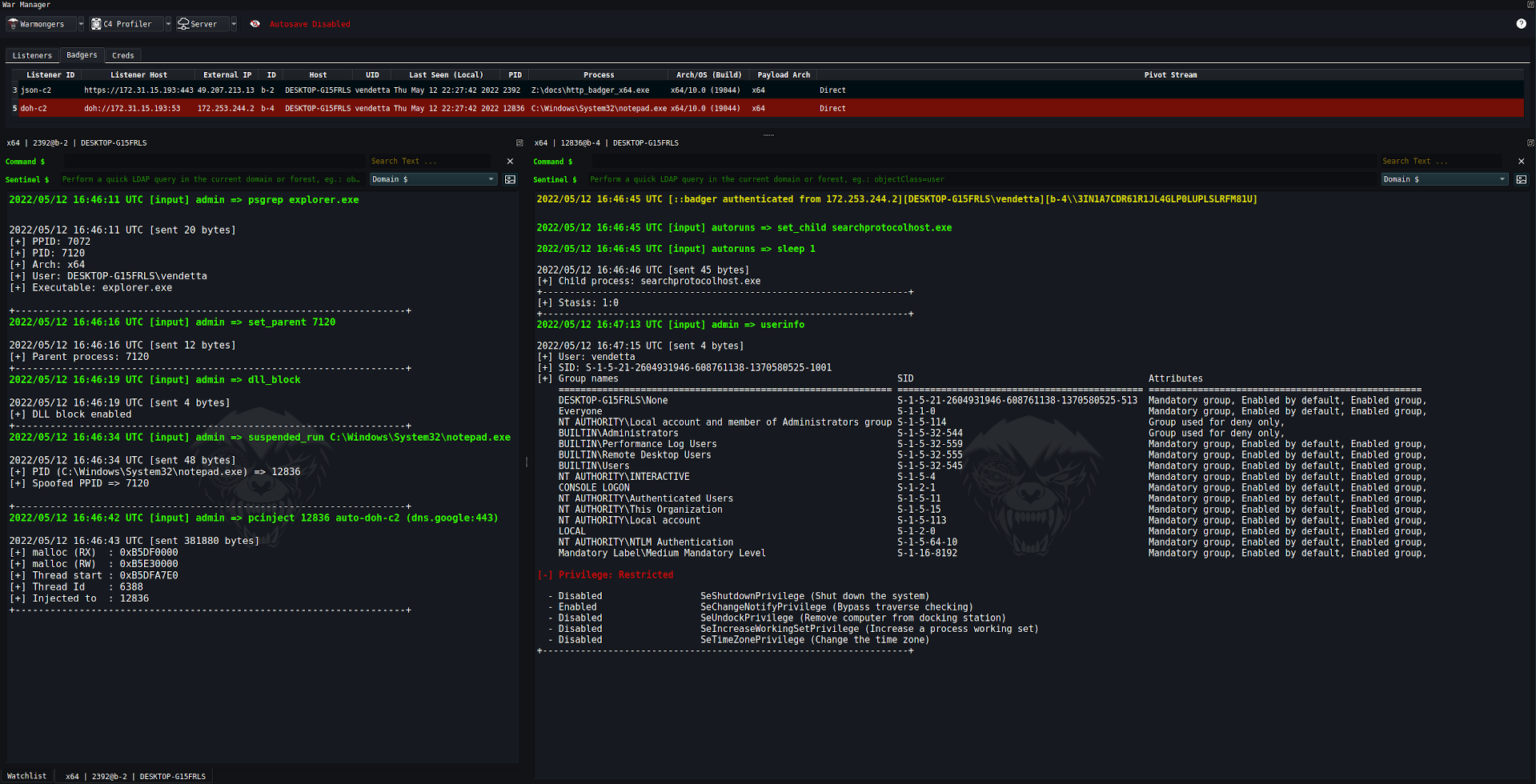
Brute Ratel: Marketed as a “Customizable Command and Control Center” or “C4” framework that provides a true adversary simulation-like experience and was created by Chetan Nayak or Paranoid Ninja.
- C2 Matrix: This is not a framework, but a comprehensive list of all C2 frameworks available, it is currently being maintained by Jorge Orchilles and Bryson Bort and I highly recommend you to check it out.
This was a small glimpse of Command and Control attacks and frameworks, there are plenty more to cover, like how to set up a C2 server and how to start an attack, but that is out of the scope of this story. Keep an eye out on the wild interwebs for the next stories.
[story continues]
tags