TL;DR —
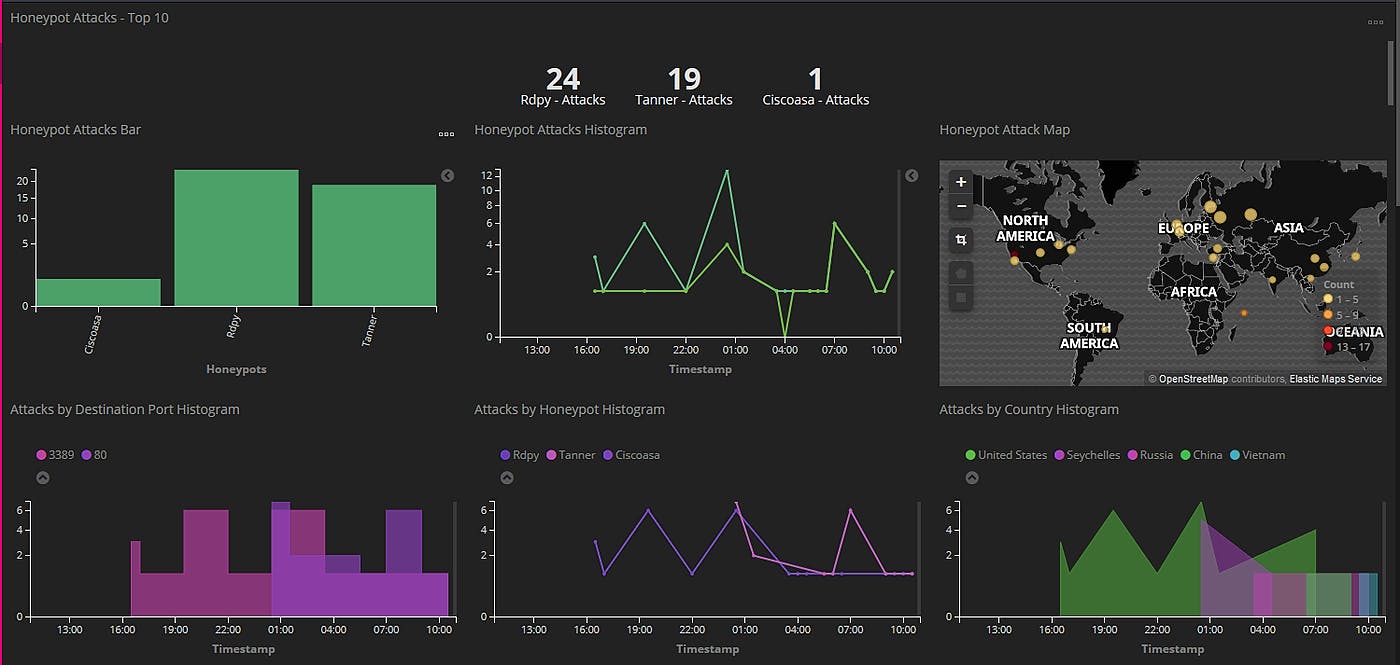
A honeypot is a system, whose sole purpose is to attract potential intruders and record their activity, to further analyse and investigate security breaches. For companies, having a honeypot can be a useful data resource and also an excellent threat hunting exercise. It is also possible to build personalised honeypots mimicking a companies environment to further entice attackers by hosting a fake active directory for example. Understanding who wants to attack you, will also help you prepare your defences. It took 16 minutes before I had my first honeypot attack.
[story continues]
Written by
@stephen-chapendama
I'm a Technology Manager @ Foundervine.com
Topics and
tags
tags
google-cloud-platform|kibana|elasticsearch|honeypot|cybersecurity|security-incident-management|google|t-mobile
This story on HackerNoon has a decentralized backup on Sia.
Transaction ID: A050GY8cnn-0UcnAcmAdHwyaH5xzKpaMhpUTKpnd4Vg