⚠️ Note
This content is meant purely for learning and research purposes. Avoid testing vulnerabilities on public blockchains. Always follow responsible disclosure practices when identifying bugs in smart contracts.
👋 Hello everyone, I’m Vinay Sati — a Bug Bounty Hunter, Forensic Investigator, and Web3 Security Tester.
I consider myself a versatile cybersecurity professional, passionate about finding vulnerabilities, securing smart contracts, and investigating digital threats. In this article, I’ll share a real example of a Web3 exploit and show you how to identify and prevent such risks.
Introduction
In blockchain development, smart contracts may encounter serious vulnerabilities, especially when:
- There’s a loop that iterates over data provided by users
- The array input length is not limited
- Proper permissions or access control are missing
These issues can result in the contract becoming unusable, gas being wasted, or potential abuse by malicious actors.
Let's look at a clear example of this kind of vulnerability, along with a simplified code sample.
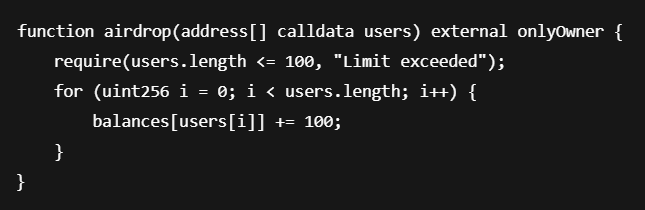
Vulnerable Smart Contract Example
Below is a contract that simulates a basic batch airdrop. However, it contains a key flaw:
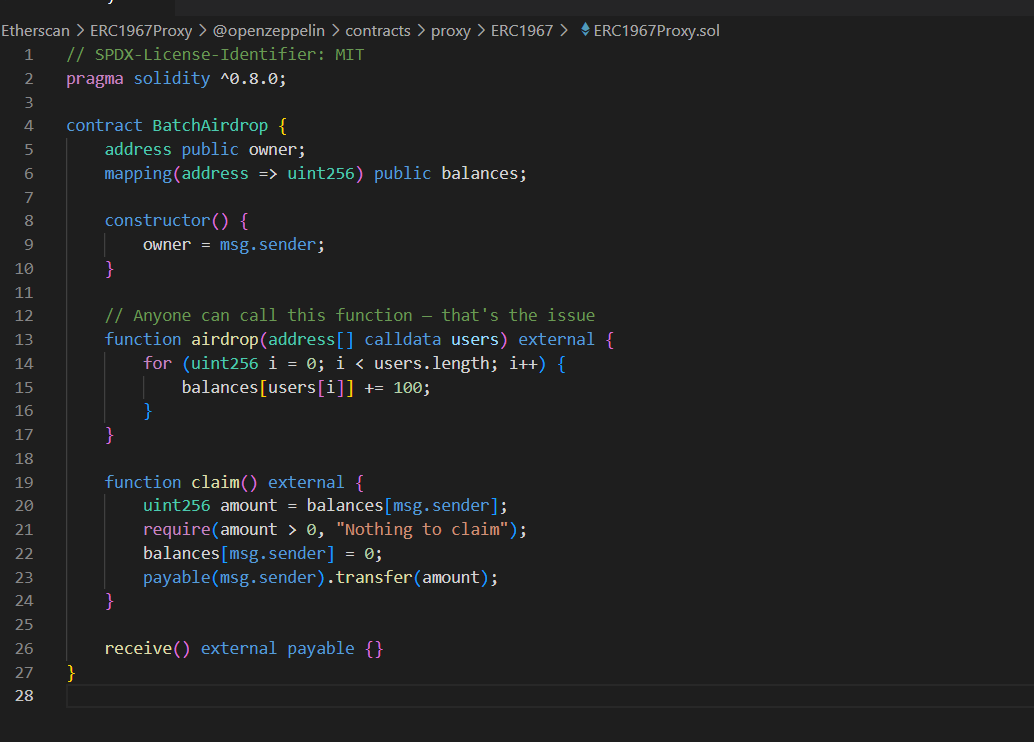
💀 What Could Go Wrong?
No restriction on who can call the airdrop() function.
No limit on the number of addresses passed into the function.
Someone could pass in thousands of addresses, causing the loop to consume all available gas.
This can disable the contract's functionality or cause ETH to be locked due to failed execution.
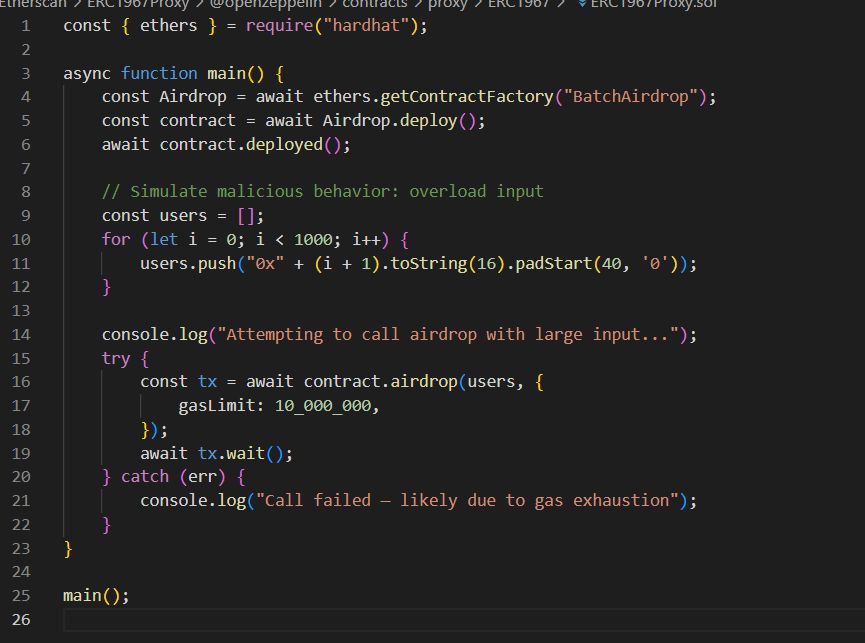
🧪 Simulating the Exploit (In a Test Environment)
Here’s an example using a development framework that demonstrates how this kind of exploit might occur:
🛡️ How Can This Be Fixed?
✅ Add Access Restrictions
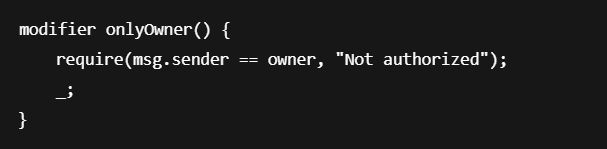
Update the vulnerable function like this:
🧯 Summary of Fixes
|
Fix |
Purpose |
|---|---|
|
Add |
Prevent unauthorized access to core logic |
|
Add input length check |
Avoid gas exhaustion through oversized loops |
|
Consider off-chain batching |
Handle large distributions more safely |
📸 Visual Aids (Optional for Reports)
-
Attack Flow Diagram: User ➜ Calls vulnerable function ➜ Contract loops ➜ Exceeds gas ➜ Fails
-
Before vs. After code comparison (highlighting secure access control)
🚀 Real Examples
|
Project |
Vulnerability |
Outcome |
|---|---|---|
|
Akropolis |
Reentrancy + logic flaw |
~$2M lost |
|
Bancor |
Infinite loop DoS |
250 ETH bounty awarded |
|
DYDX |
Gas griefing + front-running |
Resolved via bug report |
🙌 Final Thoughts
Even basic oversights like failing to limit array sizes or restricting function access can result in major vulnerabilities. Taking the time to audit code, simulate edge cases, and follow best practices helps protect users and build trust in decentralized systems.
[story continues]
tags