TL;DR —
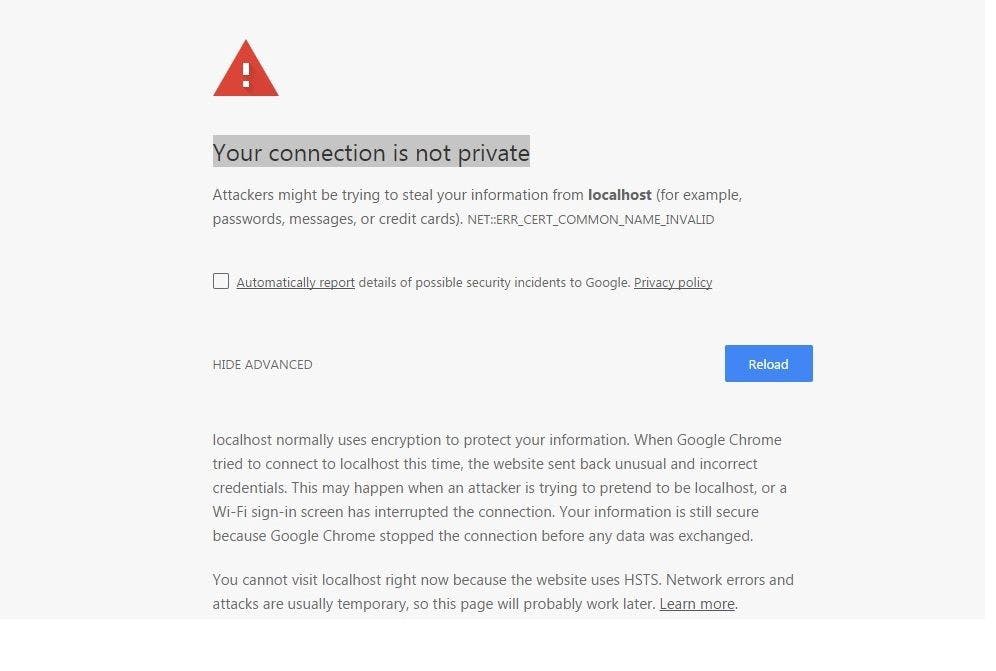
Certificate chains are used to be able to verify an end user certificate against a list of intermediaries and a root authority. Common certificate authorities, such as Verisign, DigiCert, and Entrust, are automatically trusted by most browsers. However, if you use an untrusted internal certificate authority to generate SSL certificates for internal resources, you will be nagged by your browser when you attempt to connect. The certificate chain enables the receiver to verify that the receiver is trustworthy, but if the certificate chain is invalid or broken, your certificate will not be trusted by some devices.
[story continues]
Written by
@digitalbeardy
☁️ Cloud Software Consultant 🖊️ #DevOps 🚀 #Serverless ⚡#Javascript 🔥 #DotNet 👊 #MachineLearning
Topics and
tags
tags
ssl-certificate|security|networking|http|dns|ssl|backend|search-engine|web-monetization
This story on HackerNoon has a decentralized backup on Sia.
Transaction ID: xcs5aPbEyu-bDRB90xzd4ISYD7Yy_HHZa8HqCpmSj8E