TL;DR —
This section of the article delves into the diffusion equation, a fundamental aspect of chaotic video encryption. Understanding this equation is crucial for grasping encryption techniques and ensuring robust security in chaotic systems.
Authors:
(1) Dong Jiang, School of Internet, Anhui University, National Engineering Research Center of Agro-Ecological Big Data Analysis and Application, Anhui University & jiangd@nju.edu.cn;
(2) Zhen Yuan, School of Internet, Anhui University;
(3) Wen-xin Li, School of Internet, Anhui University;
(4) Liang-liang Lu, Key Laboratory of Optoelectronic Technology of Jiangsu Province, Nanjing Normal University, National Laboratory of Solid State Microstructures, Nanjing University, Nanjing & lianglianglu@nju.edu.cn.
Table of Links
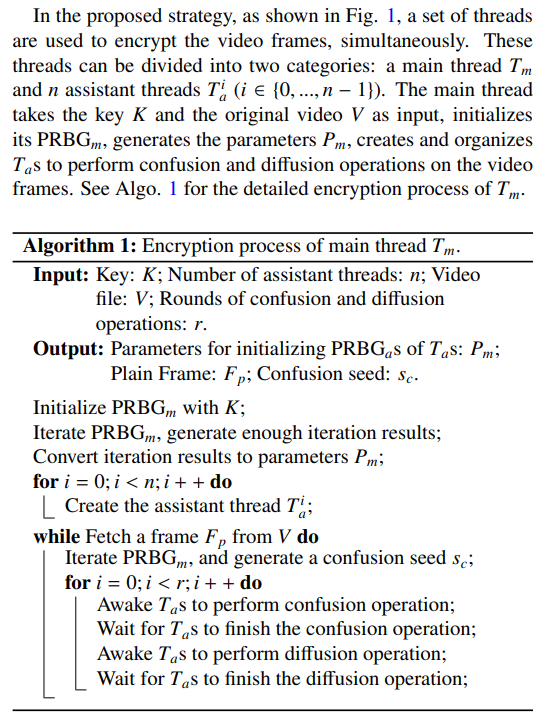
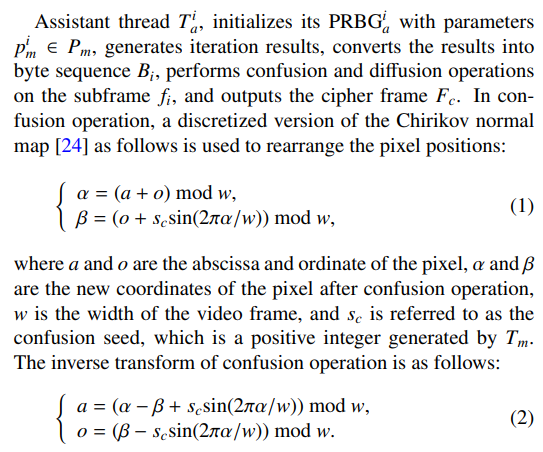
2. Strategy Description
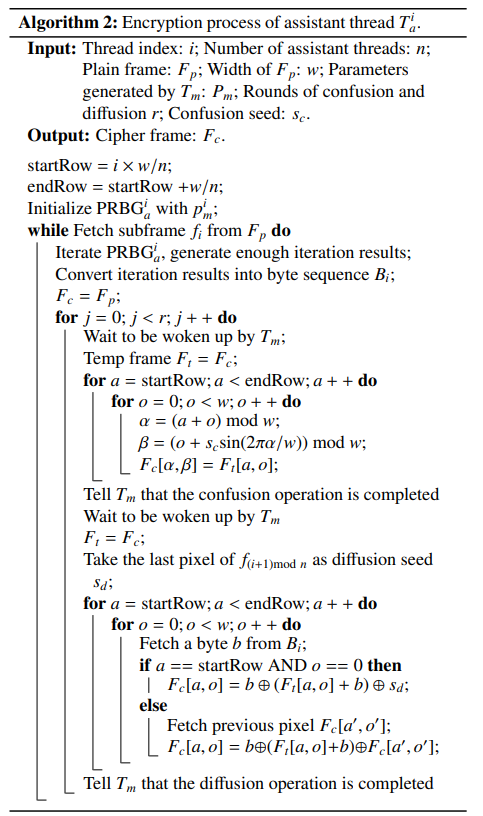
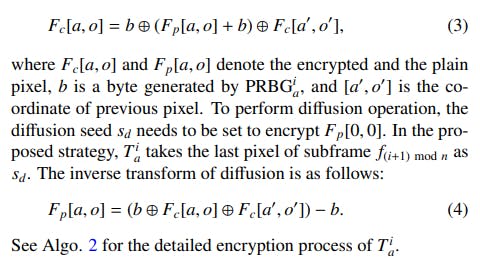
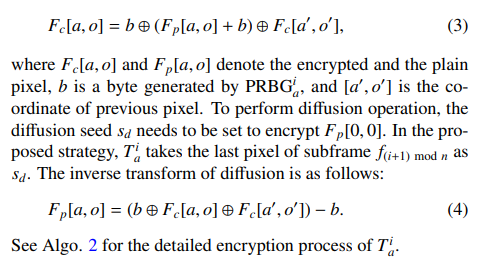
In diffusion, the following equation is employed[25]:
This paper is available on arxiv under CC 4.0 license.
[story continues]
Written by
@multithreading
Research to enable more than one user at a time without requiring multiple copies of the program running on the computer
Topics and
tags
tags
video-encryption|real-time-video-encryption|parallel-computing|confusion-and-diffusion|chaotic-systems|multi-threaded-encryption|cryptographic-algorithms|video-encryption-methods
This story on HackerNoon has a decentralized backup on Sia.
Transaction ID: _VQSii_vOMCR4h6ZQ4HM4iBHnuRECZvAdESGZSnAEts