TL;DR —
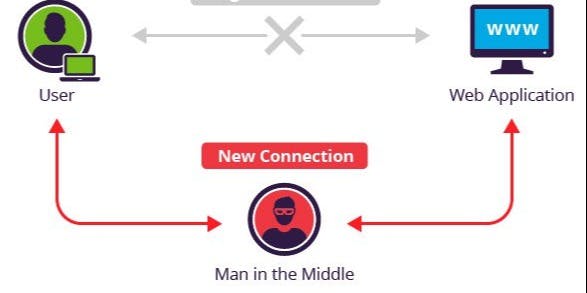
MitM attacks are the type of attacks where the attacker eavesdrop between two communicating hosts by putting himself in between the point of data transmission. This allows the attacker to “Listen” to what the hosts are communicating and “Read” them. MitM is performed to steal credit card information, login credentials, data manipulation, Identity theft and so on and so forth. Most of this attack is performed in Open WiFi Hotspots in Bus stations, Railway stations or maybe at the nearest Starbucks.
[story continues]
Written by
@heller_9
A versatile and motivated professional with an ardent interest in Cyber Security and Music Product
Topics and
tags
tags
security|https|man-in-the-middle|mitm|vpn|latest-tech-stories|man-in-the-middle-attack|eavesdropping
This story on HackerNoon has a decentralized backup on Sia.
Transaction ID: gqreU8FYivR3-F1RvTqAkrzuX6unQNDF74aef8utFTI