We have all been there. You are standing at the grocery store checkout or perhaps the ticket booth at a theater. You simply tap your phone against the terminal. A second later, the payment is verified. It feels like magic, but underneath that smooth user experience is a complex web of security protocols designed to keep your money safe.
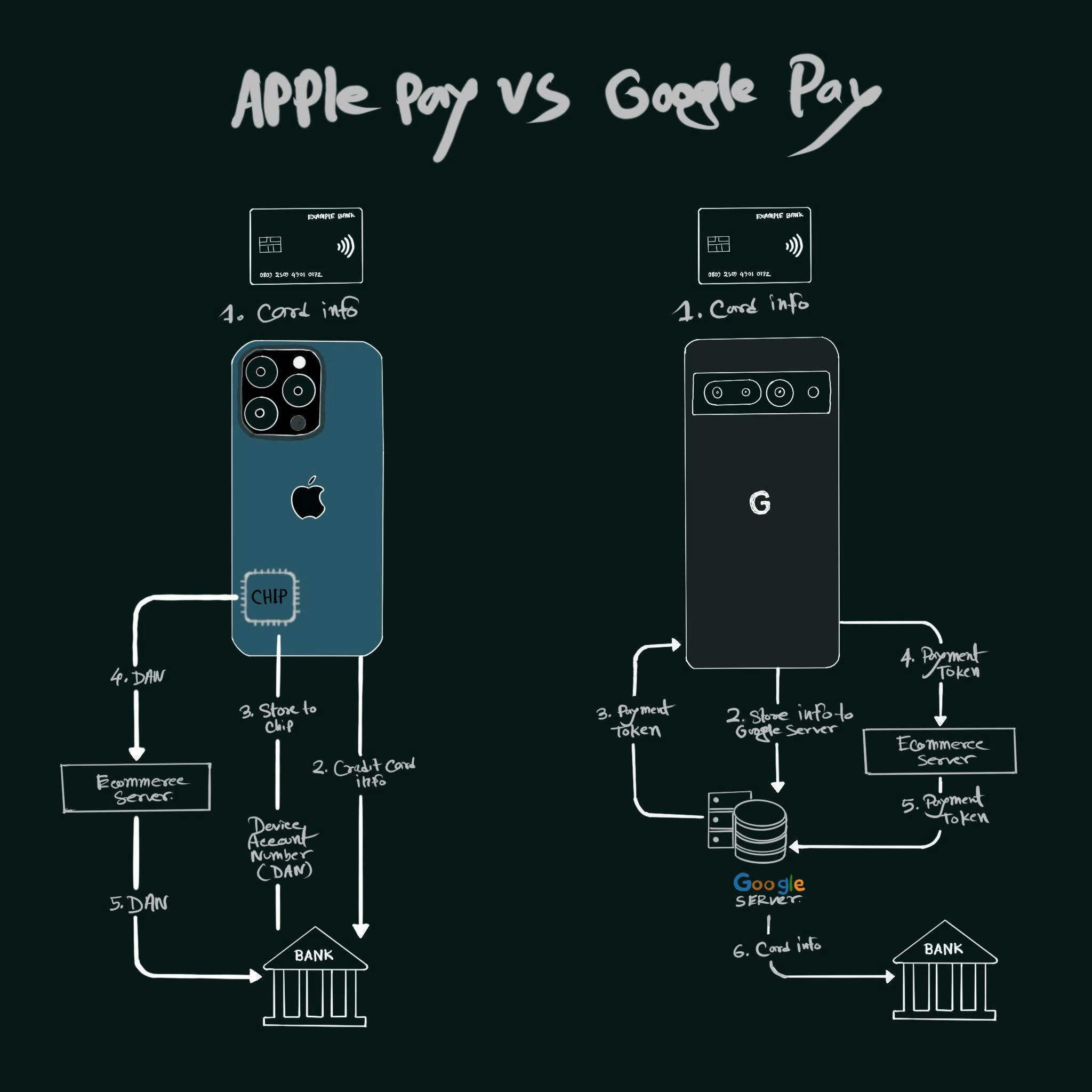
While the end result looks identical on your screen, the plumbing behind Apple Pay and Google Pay is fundamentally different. One treats your phone like a physical safe, while the other treats it like a gateway to a secure cloud.
The Apple Way: A Vault in Your Pocket
Apple Pay is built on the philosophy of local hardware security. When you add a credit card to your iPhone, the device does not just store your card number in a folder somewhere. Instead, it reaches out to your bank. The bank then issues a unique replacement number known as a Device Account Number or DAN.
This is where the hardware comes in. That DAN is stored inside a specialized piece of silicon called the Secure Enclave. Think of this as a tiny, isolated computer inside your phone that only handles the most sensitive data.
The process looks like this:
- Your phone generates a single use cryptographic code.
- It sends that code along with your DAN to the merchant.
- The merchant passes this to the bank.
- The bank verifies that the DAN belongs to your phone and the code is valid.
At no point does your real card number ever touch the merchant system. In fact, your real card number is not even on the Apple servers. It is strictly a conversation between your phone and your bank. It is basically: phone → bank → done. Everything sensitive stays on the device.
The Google Way: The Power of the Cloud
Google Pay takes a different path that leans heavily into the flexibility of the cloud. While it still hides your real card details from the shop, it does not rely as much on a specific hardware chip to hold the keys to the kingdom.
Instead, Google uses what is known as cloud tokenization. Your card information is linked to the secure servers at Google. When you go to pay, the system fetches or creates a payment token.
The flow looks more like this:
- Your phone communicates with a Google server.
- The server generates a secure token for the transaction.
- That token is sent to the merchant and then validated by the bank via Google.
Because Google manages the tokens in the cloud, the system is incredibly flexible. It works across a much wider range of devices because it does not require every single phone to have a specific type of high end security chip like the Secure Enclave. It is more like: phone → Google server → bank.
The Great Comparison: Hardware vs Software
To help you visualize the difference, we can look at how they manage the lock on your data.
| Feature | Apple Pay | Google Pay |
| Primary Storage | On device hardware chip | Secure Google servers |
| Security Philosophy | Localized isolation | Cloud based tokenization |
| Data Residency | DAN stays on the phone | Tokens managed in the cloud |
| System Flow | Phone to Bank | Phone to Google to Bank |
| Privacy Focus | Apple never sees transaction data | Google handles the token flow |
Why Both Are Better Than Plastic
Regardless of which side of the fence you are on, both of these systems are leagues ahead of a physical plastic card. When you swipe or dip a traditional card, you are handing over your real name, your real card number, and your security code. If that merchant database gets hacked, your details are out in the wild.
With mobile payments, the merchant gets a temporary alias. Even if a hacker steals the data from the store, they only get a useless DAN or a token that has already expired.
The Simple Takeaway:
Apple Pay locks your card inside your phone.
Google Pay locks your card behind the Google servers.
Both methods ensure that your actual financial identity remains invisible to the person behind the counter. Whether you trust the Safe in your Pocket or the Vault in the Cloud is up to you, but either way, your wallet has never been more secure